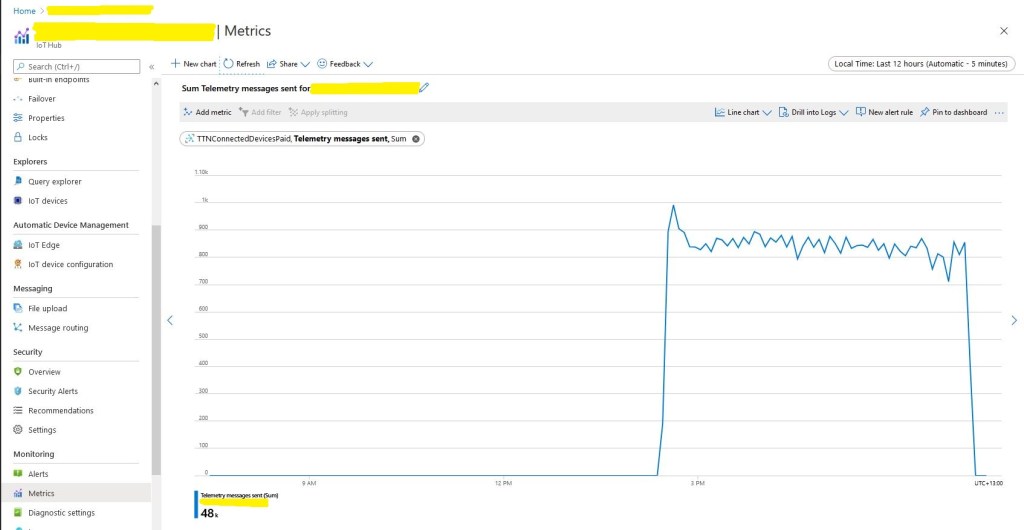
Basic Telemetry
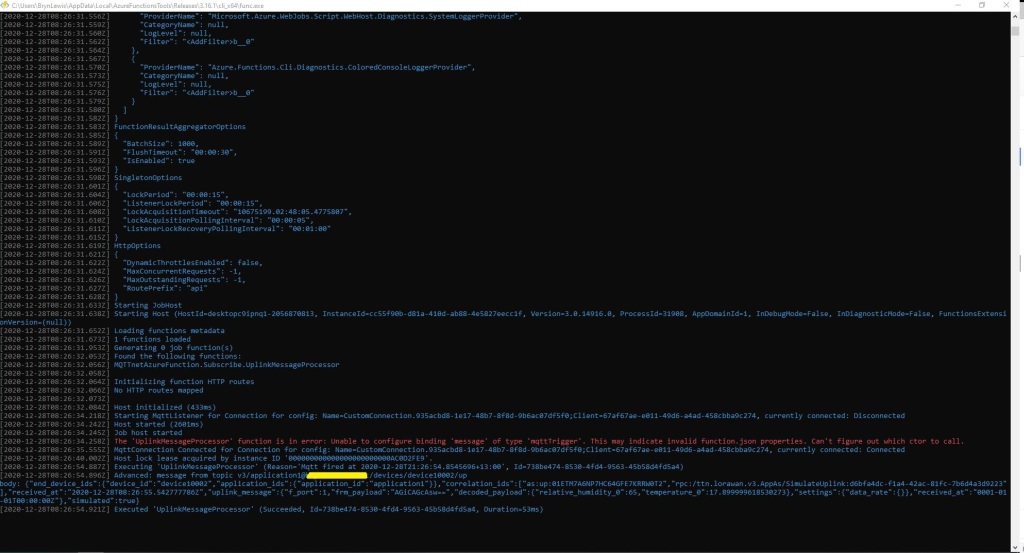
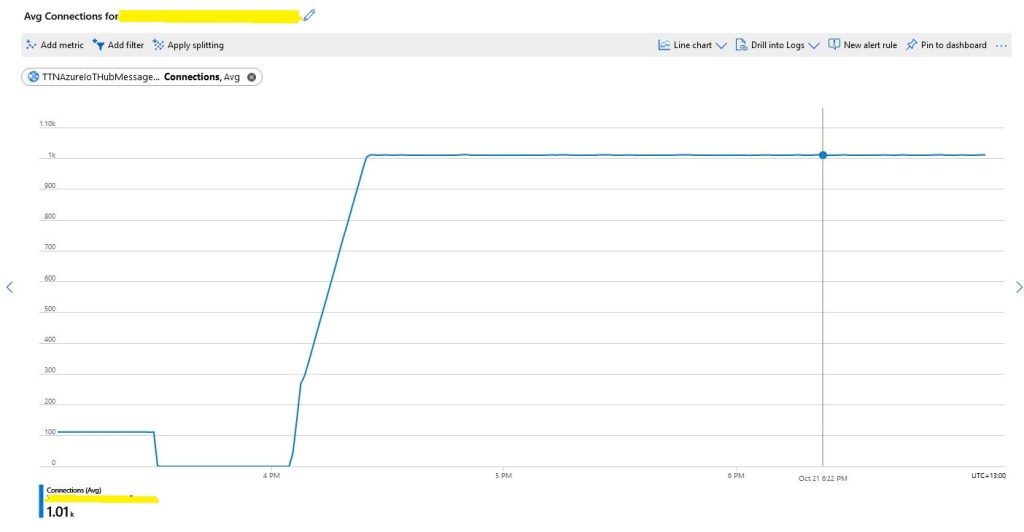
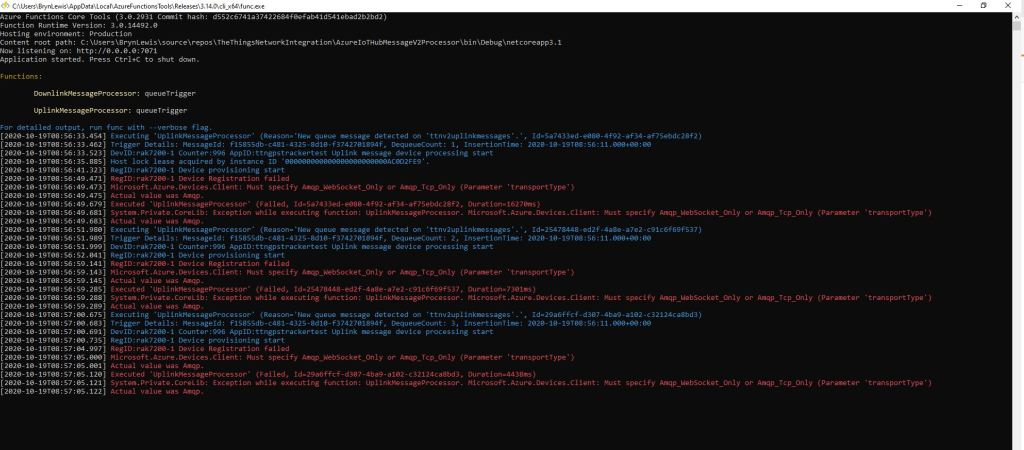
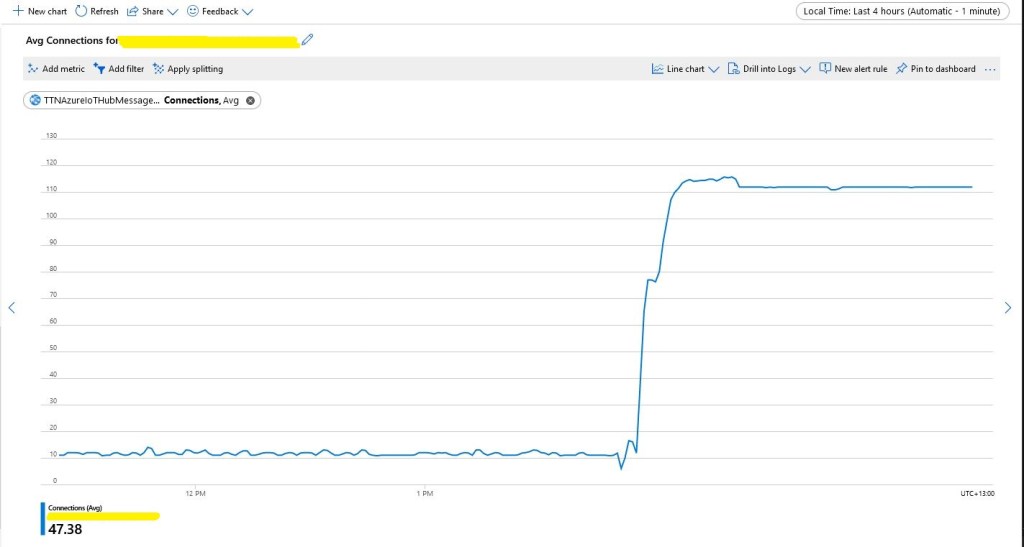
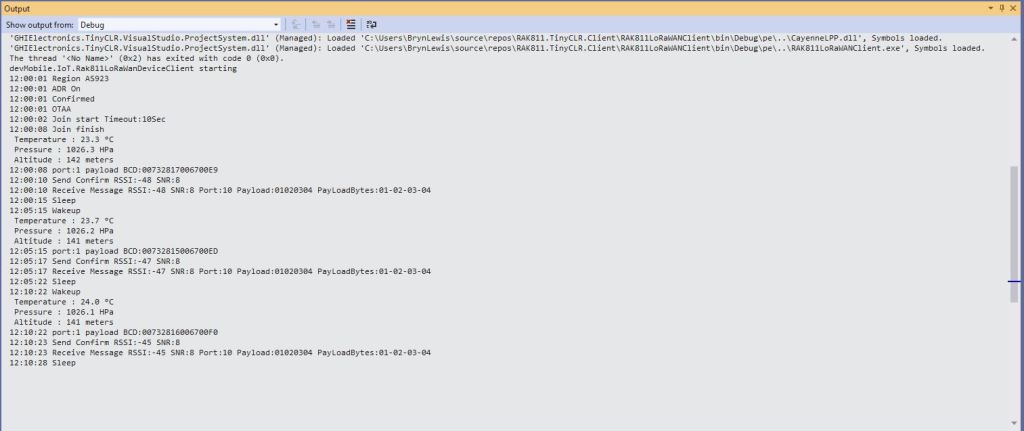
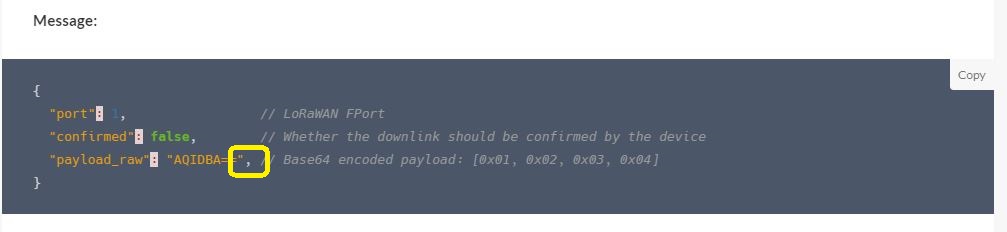
I have been struggling with making The Things Network(TTN) and The Things Industries(TTI) uplink/downlink messages Azure IoT Central compatible. To explore the messaging approaches used I have built a proof of Concept(PoC) application which simulates TTN/TTI connectivity to an Azure IoT Hub, or Azure IoT Central.
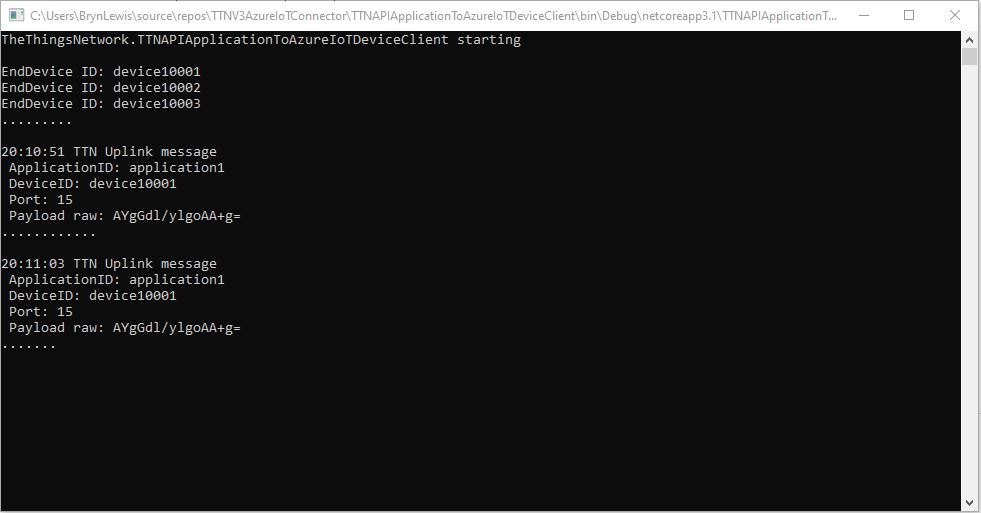
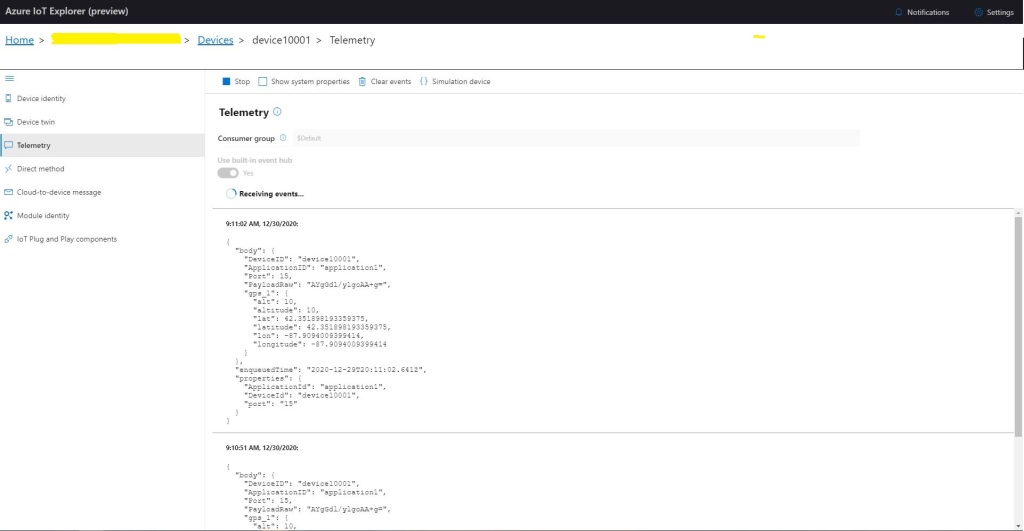
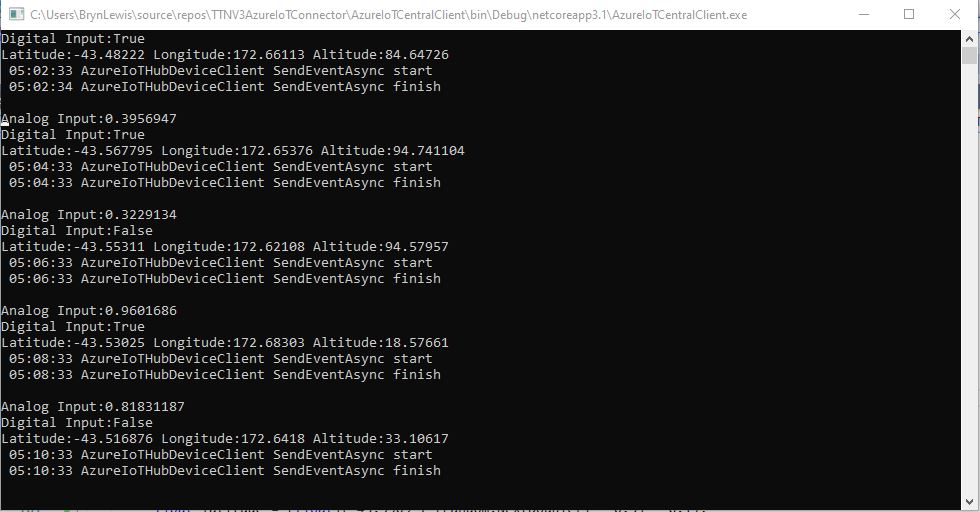
My “nasty” console application uses the Azure DeviceClient library (Advanced Message Queuing Protocol(AMQP) connectivity) to explore how to interface with Azure IoT Central. This first blog post is about to Device Cloud(D2C) telemetry
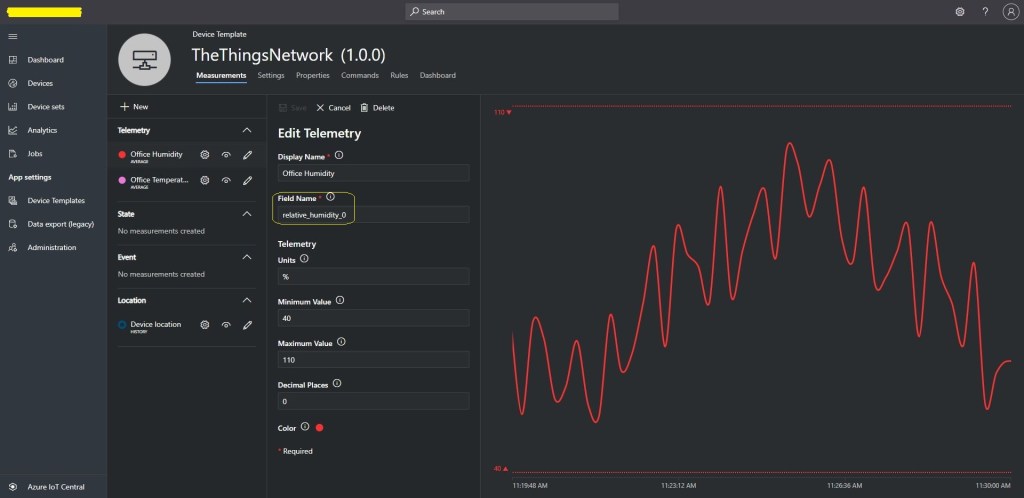
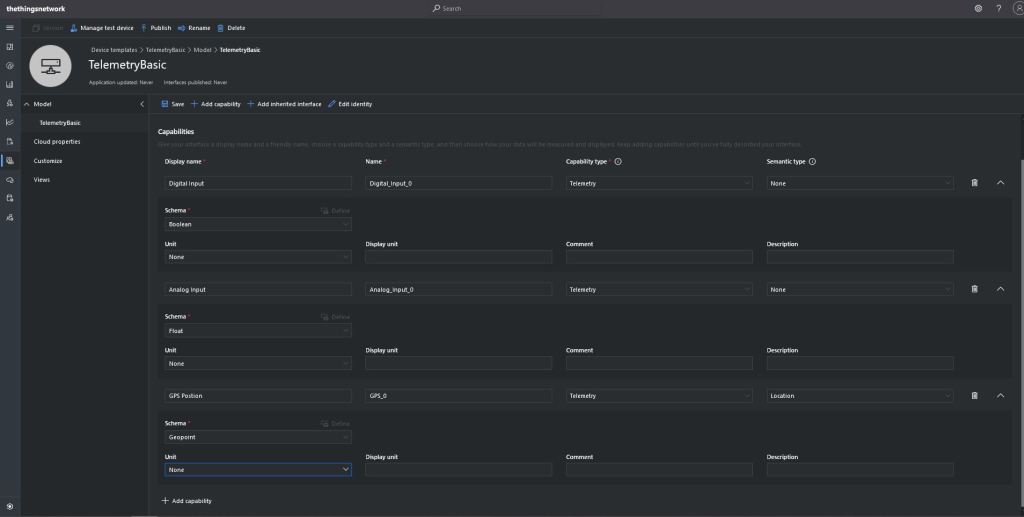
The first step was to create an Azure IoT Central Device Template with a selection of telemetry capabilities.
I then created a Plain old Common Language Runtime(CLR) object(PoCo) with Newtonsoft JSON library attributes to fine tune the serialisation/deserialation.
public class GPSPosition
{
[JsonProperty("lat")]
public float Latitude { get; set; }
[JsonProperty("lon")]
public float Longitude { get; set; }
[JsonProperty("alt")]
public float Altitude { get; set; }
}
public class DigitialTelemetryPayload
{
[JsonProperty("Digital_Input_0")]
public bool DigitalInput { get; set; }
[JsonProperty("Analog_Input_0")]
public float AnalogInput { get; set; }
[JsonProperty("GPS_0")]
public GPSPosition GPSPosition { get; set; }
}
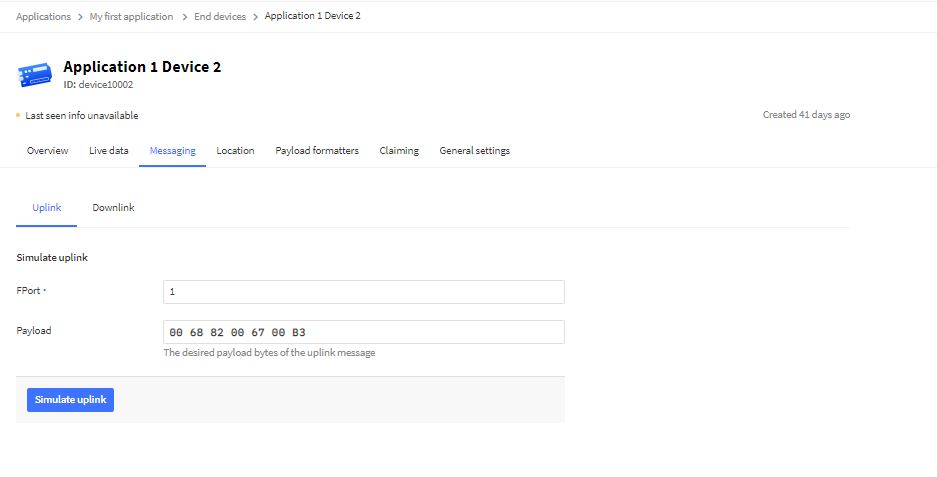
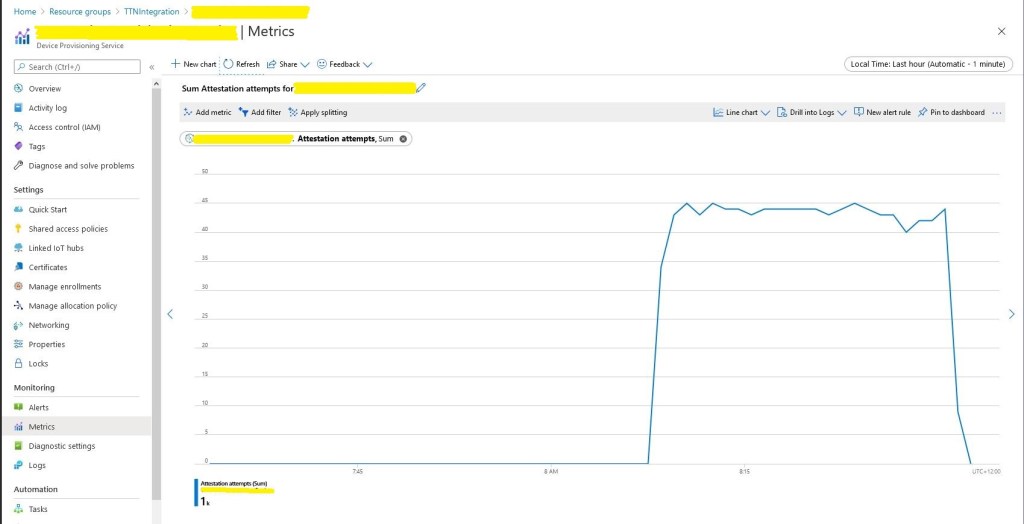
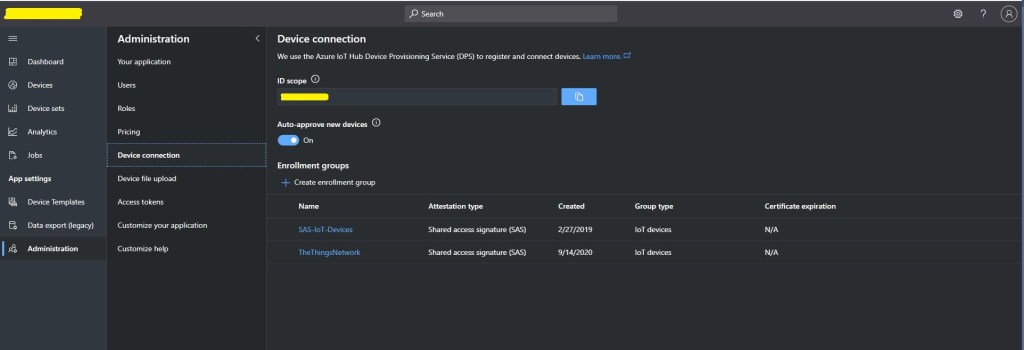
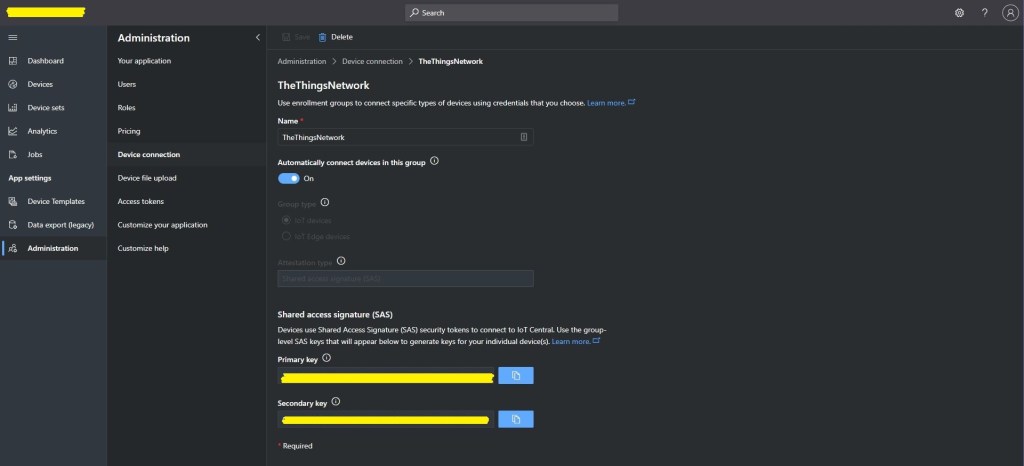
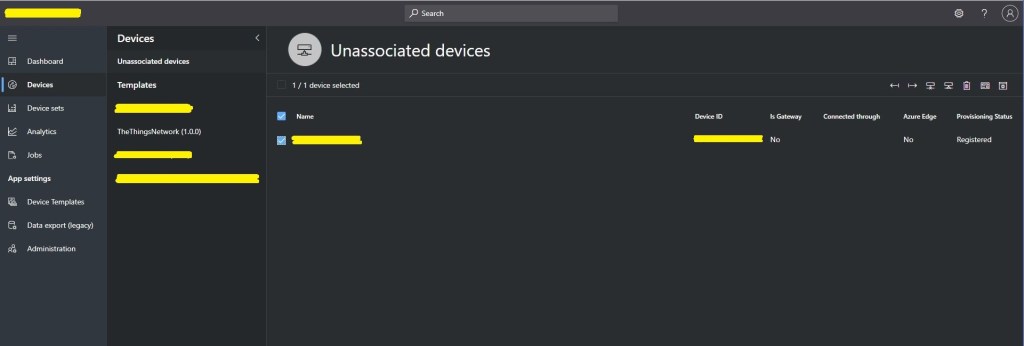
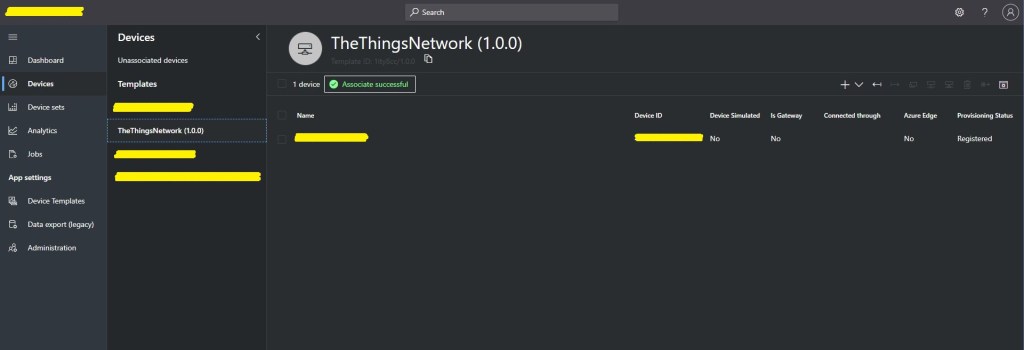
I created five devices and generated their connection strings using the DPS individual enrollment functionality of one my other sample applications.
I then “migrated” the first device to my BasicTelemetry template

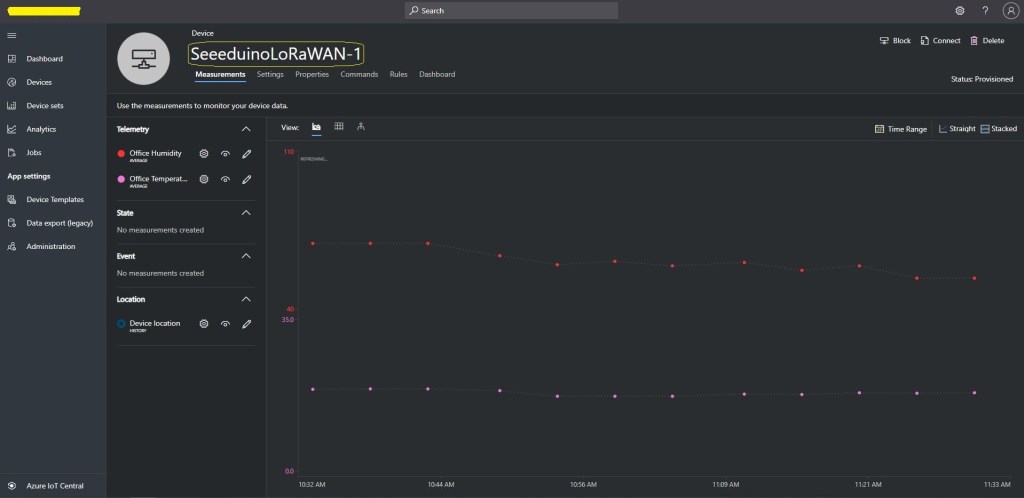
I then went back and created a Template view to visualise the telemetry from my console application.
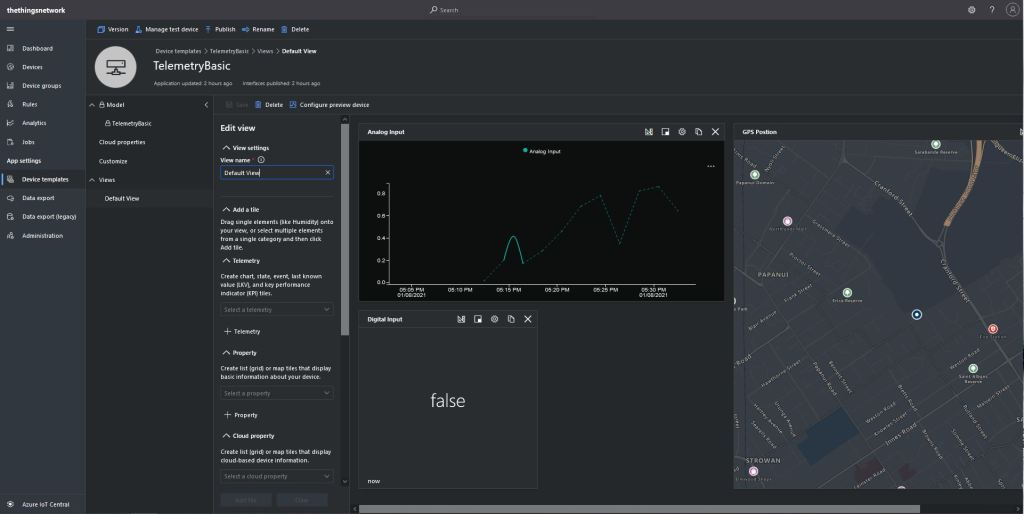
Then I configured a preview device so the template view was populated with “realistic” data.

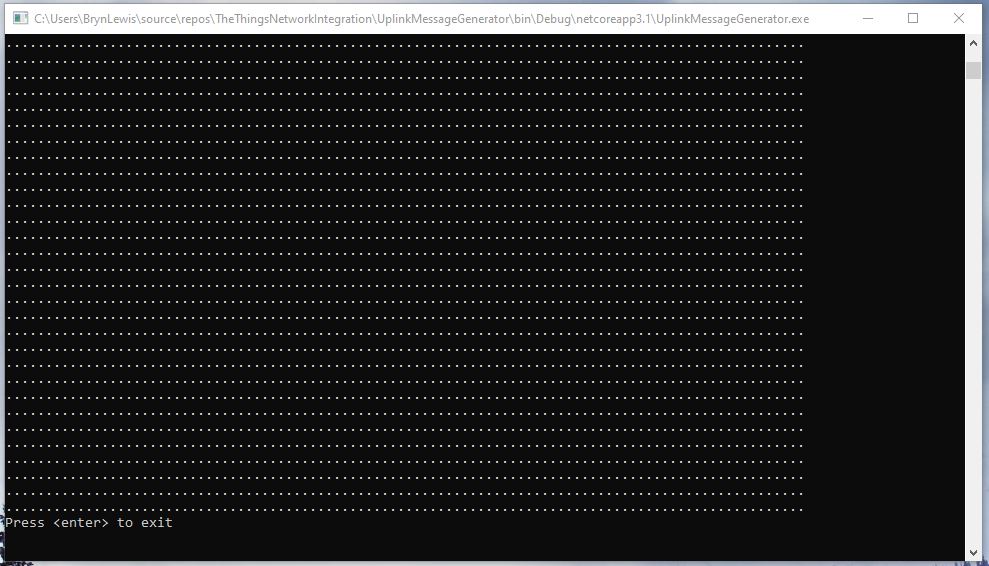
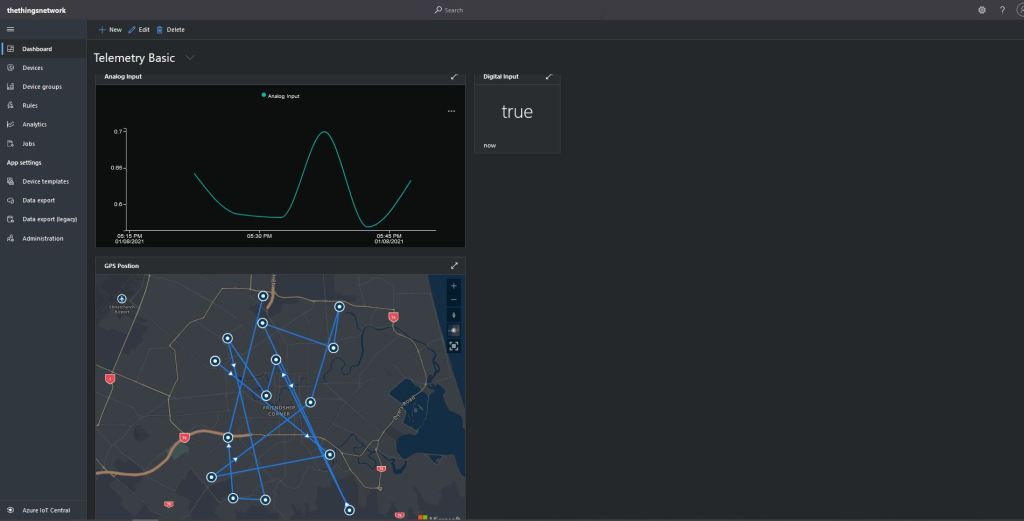
The console application simulates a digital input (random true/false), analog input (random value between 0.0 and 1.0) and a Global Positioning System(GPS) location (Christchurch Anglican Cathedral with a random latitude, longitude and altitude offset) .
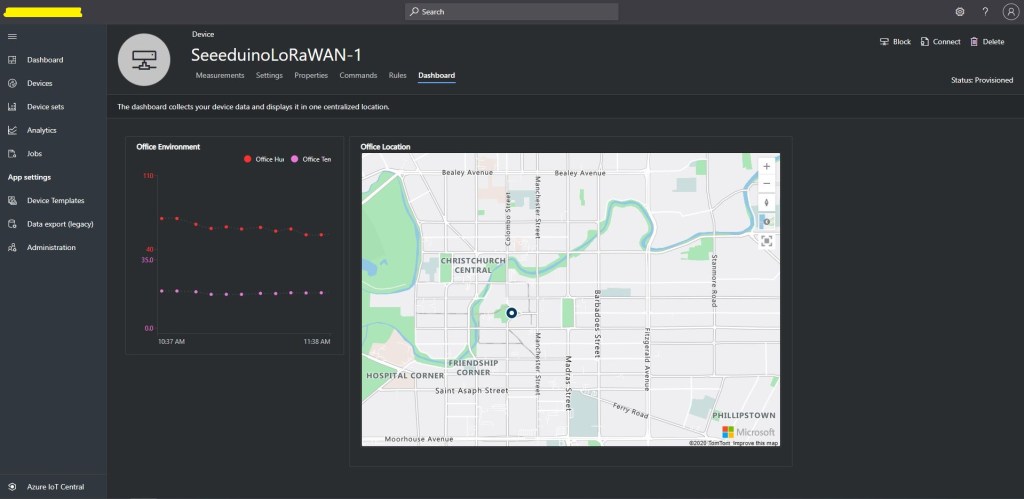
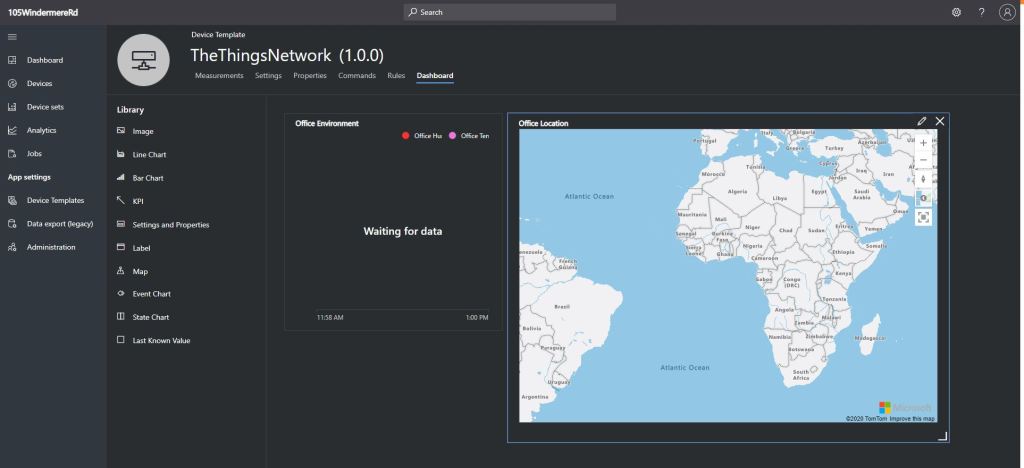
The final step was to create an Azure IoT Central Personal dashboard to visualise the data from my simulated device.
Connecting a Device, creating a Device Template, Migrating the Device, and then displaying telemetry on a personal dashboard was a good introduction to interfacing with and configuring Azure IoT Central devices.
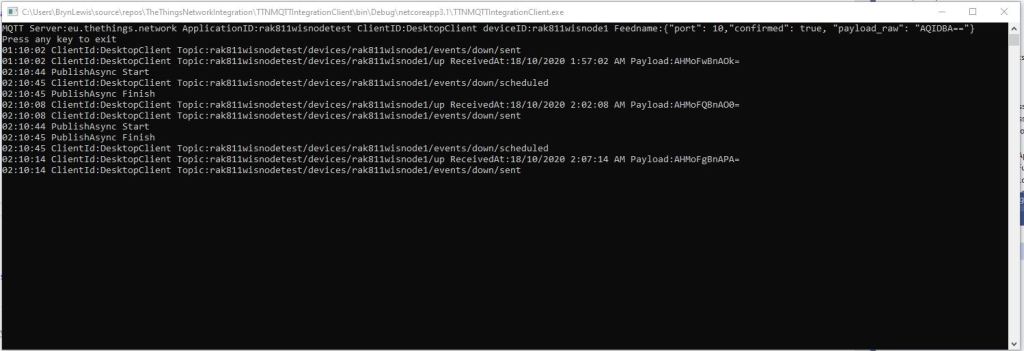
In other applications I have mapped “payload_fields” to an Azure IoT Central telemetry payload with minimal code.
{
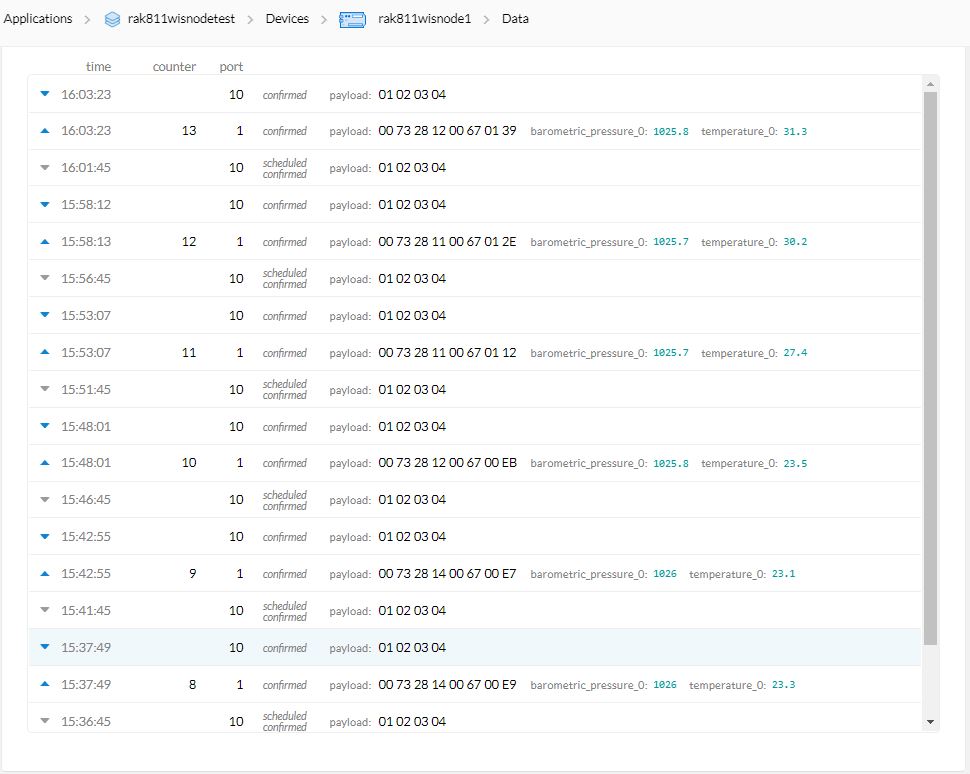
"app_id": "rak811wisnodetest",
"dev_id": "seeeduinolorawan4",
"hardware_serial": "1234567890123456",
"port": 10,
"counter": 1,
"is_retry": true,
"payload_raw": "AWcBEAFlAGQBAAEBAgAyAYgAqYgGIxgBJuw=",
"payload_fields": {
"analog_in_1": 0.5,
"digital_in_1": 1,
"gps_1": {
"altitude": 755,
"latitude": 4.34,
"longitude": 40.22
},
"luminosity_1": 100,
"temperature_1": 27.2
},
"metadata": {
"time": "2020-08-28T10:41:04.496594225Z",
"frequency": 923.4,
"modulation": "LORA",
"data_rate": "SF12BW125",
"coding_rate": "4/5",
"gateways": [
{
"gtw_id": "eui-b827ebfffe6c279d",
"timestamp": 3971612260,
"time": "2020-08-28T10:41:03.313471Z",
"channel": 1,
"rssi": -53,
"snr": 11.2,
"rf_chain": 0,
"latitude": -43.49885,
"longitude": 172.60095,
"altitude": 25
}
]
},
"downlink_url": "https://integrations.thethingsnetwork.org/ttn-eu/api/v2/down/rak811wisnodetest/azure-webapi-endpoint?key=ttn-account-v2.12345678901234567_12345_1234567-dduo"
}
This was a longish post with lots of screen shots so I don’t have to repeat core setup instructions in future posts.