I now have a GHI Wifi RS21 Module which I needed get working with a FEZ Spider running NetMF 4.2 (I have upgraded both my FEZ Spiders to 4.2 so no 4.1 vs. 4.2 comparison this time). Other developers seemed to be struggling to get connectivity with various earlier versions of the NetMF going working robustly.
(http://www.tinyclr.com/forum/topic?id=9404)
(http://www.tinyclr.com/forum/topic?id=9388)
(http://www.tinyclr.com/forum/topic?id=9502)
(http://www.tinyclr.com/forum/topic?id=9538)
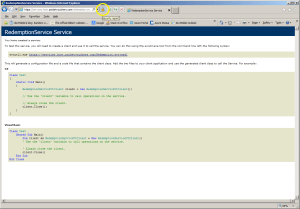
So after flashing my device to 4.2.9.0 I built a quick and dirty demo to illustrate how I got my RS9110 based Wifi module working with designer support. For a real application I would move the initialisation out of the ProgramStarted and improve the exception handling but this sample code should be enough to get you started. I have checked and this code works after both a device reset or re-flashing.